I’m trying to connect from clientless devices on my home network to a remote peer on a VPS. I have a local peer in an LXC which I’m routing traffic through.
The route is:
Clientless laptop (192.168.6.0/24) → Router (Unifi gateway) (192.168.6.1/24) → Local peer [Netbird network] (10.70.0.3/24) → Remote peer
I have route on the Unifi gateway to route the Netbird subnet via the local peer 10.70.0.3.
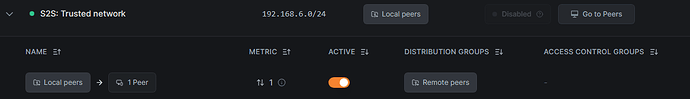
I have a network route in place for this with a Peer Group containing just the local peer, and a distribution group containing just the remote peer (although I intend to add others once it works).
I have access policies allowing traffic in both directions.
The following works fine:
- connectivity from local peer to remote peer and vice versa
- connectivity from the remote peer to local clientless devices (192.168.6.0/24) via the local peer, onward routed through the Unifi gateway.
- routing from the local clientless devices to the remote peer when masquerade is enabled
But, when I disable masquerade:
- packets reach the remote peer with their original source address and can be seen with tcpdump -i wt0
- packets are dropped in the kernel before being processed, i.e. no response to ICMP or SSH
- tcpdump shows no response packet
- netbird status -d on the remote peer shows the correct route:
Networks: 192.168.6.0/24
Thanks in advance for any advice.
A clear and concise description of what the problem is.
As above
Steps to reproduce the behavior:
As above
Expected behavior
As the routes and access policies are present and routing works in the other direction, I’d have expected to be able to be able to route from my local clientless device to the remote peer without masquerading.
Are you using NetBird Cloud?
NetBird Cloud
0.66.0
Is any other VPN software installed?
No
Debug output
I’ve collected this and can provide to support if required.
Screenshots
See above
Additional context
N/A
Have you tried these troubleshooting steps?
- Reviewed client troubleshooting (if applicable)
- Checked for newer NetBird versions
- Searched for similar issues on GitHub (including closed ones)
- Restarted the NetBird client
- Disabled other VPN software
- Checked firewall settings